Helios BYOC
On this page
For customers that want a managed experience like SingleStore Helios, but have data sovereignty and tenancy restrictions due to compliance or contractual reasons, SingleStore offers Helios Bring Your Own Cloud (BYOC).
Why Use Helios BYOC
Helios BYOC brings the fully managed cloud experience to the customer's own AWS VPC with the following benefits:
-
Operational management
-
Create, suspend, and resume workspaces through the SingleStore Cloud Portal
-
Out-of-the-box Grafana dashboards for workspace monitoring
-
-
Scalability and reliability
-
Scale workspaces using the Cloud Portal
-
Auto healing in the event of node failure
-
A variety of scaling mechanisms for dynamic workloads, such as auto-scaling, cache scaling, and fast scaling
-
-
Resource/data management and security
-
Isolate workloads with shared data using workspaces within the customer's VPC in their AWS account
-
Organization-, workspace group-, and database-level role-based access control (RBAC)
-
Helios BYOC Architecture
Helios BYOC is designed as a modular system consisting of three distinct components:
-
Control Plane
-
Data Plane
-
Nimbus Gateway
The following is a visual representation of the Helios BYOC architecture which illustrates the primary components and how they interact with each other.
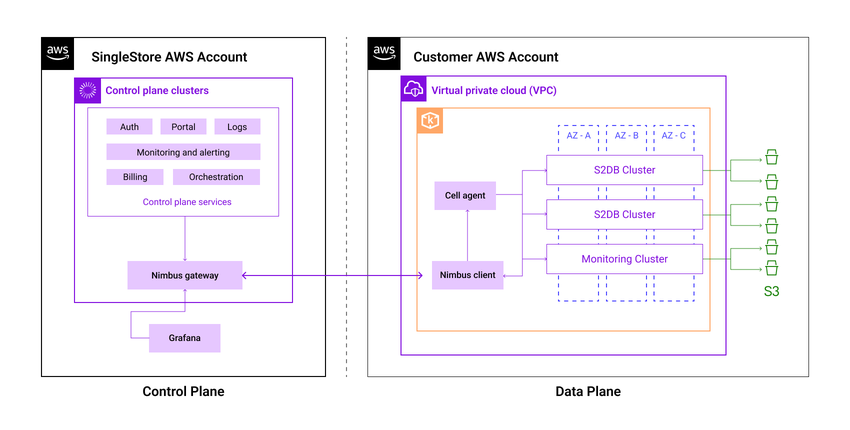
Control Plane
The Control Plane is an online portal that provides tools to manage your SingleStore workspaces, database deployments, and services in the Data Plane.
Note
From the Control Plane, the customer-hosted Data Planes are accessible only via these secure tunnels.
The Control Plane stores data on the organizations, cluster metadata, and billing information.
Data Plane
The Data Plane represents a SingleStore cell that is bootstrapped in the customer’s VPC within their AWS account.
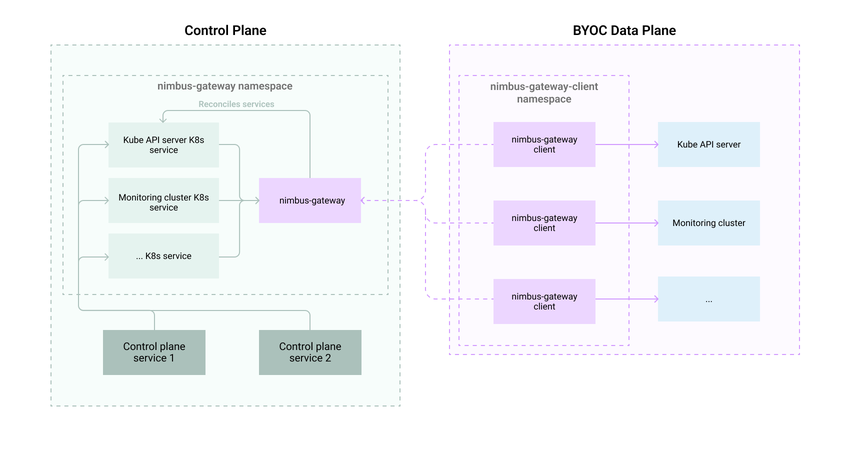
Nimbus Gateway
The Nimbus Gateway enables communication between the Control Plane and the Data Plane by establishing secure tunnels.
The following is a visual representation of the data flow via the Nimbus Gateway.
How Helios BYOC Works
Helios BYOC establishes a fully-managed cloud environment within the customer's own AWS account through the Control Plane and the Data Plane.
In this section
Last modified: June 11, 2025

